These It Security Manager OKR templates are meant to help teams move from ideas and projects to measurable business outcomes. Use them as a starting point, then tailor the metrics and initiatives to the reality of your company.
Use It Security Manager OKRs to define what success looks like this quarter, then track them weekly so the team can quickly spot blockers, learn, and adjust execution.
This page shows the top 4 of 4 templates for it security manager, with internal links to related categories and guidance for adapting the examples to your team.
Last template update in this category: 2024-07-09What this category is for
- Teams that need a clearer operating rhythm for it security manager work.
- Managers who want examples they can adapt into outcome-focused quarterly plans.
- Leaders comparing adjacent categories before choosing the best OKR direction.
Best outcomes to track
- It Security Manager priorities tied to measurable business outcomes.
- Weekly check-ins that surface blockers before they become delivery issues.
- Better alignment between initiatives and the metrics that matter.
Related categories
Use these linked categories to explore adjacent planning areas and strengthen the internal topic cluster around it security manager.
Priority hubs
It Security Manager OKR examples and templates
Start with these top 4 examples from 4 total templates in this category, then adapt the metrics and initiatives to fit your team's constraints and operating cadence.
OKRs to minimize exposure to compliance and cybersecurity threats
ObjectiveMinimize exposure to compliance and cybersecurity threats
KREnhance cybersecurity measures to decrease cyber breaches by 30%
Implement strict password policies and two-factor authentication system
Perform regular cyber security audits and fix identified vulnerabilities
Increase employee training on phishing scams and other cyber threats
KRReduce compliance violations by 20% through implementation of stricter internal processes
Conduct regular audit checks to identify potential violations
Increase frequency of internal process assessments
Implement comprehensive employee training on stricter internal processes
KRTrain 90% of employees on updated compliance rules and cyberthreat awareness
Develop an updated compliance and cyberthreat training program
Enroll all employees in the training program
Monitor employee participation rates to reach 90% completion
OKRs to implement network DLP to limit disruption and data loss
ObjectiveImplement network DLP to limit disruption and data loss
KRIncrease DLP coverage across all critical systems by 60%
Regularly review and update DLP protection strategy
Implement DLP solutions on identified systems
Identify all critical systems lacking DLP protection
KREnsure 80% of employees are trained in DLP policy compliance by end of quarter
Identify employees needing DLP policy training
Monitor and record employees' training progress
Schedule mandatory DLP compliance training sessions
KRReduce data security incidents by 40% with DLP integration
Implement DLP software across all company systems
Train employees on data loss prevention practices
Continually monitor and update DLP systems as needed
OKRs to implement and maintain SOCII compliance measures
ObjectiveEnsure ongoing SOCII compliance
KRConduct regular testing and auditing to assess SOCII compliance status
KRTrain and educate all relevant teams on SOCII compliance regulations and best practices
KRMonitor and promptly address any SOCII compliance gaps or violations identified
Establish a dedicated team to promptly address and resolve any identified SOCII compliance issues
Implement corrective measures to address identified SOCII compliance gaps promptly
Conduct regular audits to identify any SOCII compliance gaps or violations
Maintain a vigilant monitoring system to detect any new SOCII compliance violations
KRImplement and maintain necessary controls and processes to meet SOCII requirements
Conduct initial assessment of current controls and processes to identify gaps
Develop and document new controls and processes to fulfill SOCII requirements
Regularly monitor and evaluate controls and processes to ensure ongoing compliance
Train and educate employees on the importance and execution of SOCII controls
OKRs to enhance application security knowledge and awareness among teams
ObjectiveImprove application security knowledge and awareness
KRIncrease the frequency of security checklist reviews by 50%
KRConduct at least one security training session per team
KRProvide secure coding guidelines and best practices to each team
KRImplement a mandatory security certification program for all teams
How to use It Security Manager OKRs well
Strong OKRs keep the team focused on measurable outcomes instead of a long task list. That means picking a clear objective, limiting the number of competing priorities, and reviewing progress every week.
Use It Security Manager OKRs to define what success looks like this quarter, then track them weekly so the team can quickly spot blockers, learn, and adjust execution.
Choosing software to run these OKRs?
Many teams looking for it security manager OKR examples are also comparing tools to roll them out. If you want to move from examples to execution, review our OKR software comparison guide to compare the best OKR software before you commit to a platform.
Related OKR template categories
If you are building a broader plan, these related categories can help you connect it security manager work to adjacent company priorities.
- compliance OKR templates
- leadership OKR templates
- strategic planning OKR templates
- operations OKR templates
- operations team OKR templates
- sales OKR templates
More OKR templates to explore
OKRs to craft an inspiring shared company mission, vision, and core values
OKRs to streamline service requests via self-service platform
OKRs to boost ad revenue on patrika.com
OKRs to improve overall customer satisfaction
OKRs to implement effective Agile PMO transformation
OKRs to boost scrum teams' self-management and goal achievement capabilities
Not seeing what you need?
Use Tability AI to generate OKRs based on a prompt
Tability allows you to describe your goals in a prompt, and generate a fully editable OKR template in seconds.
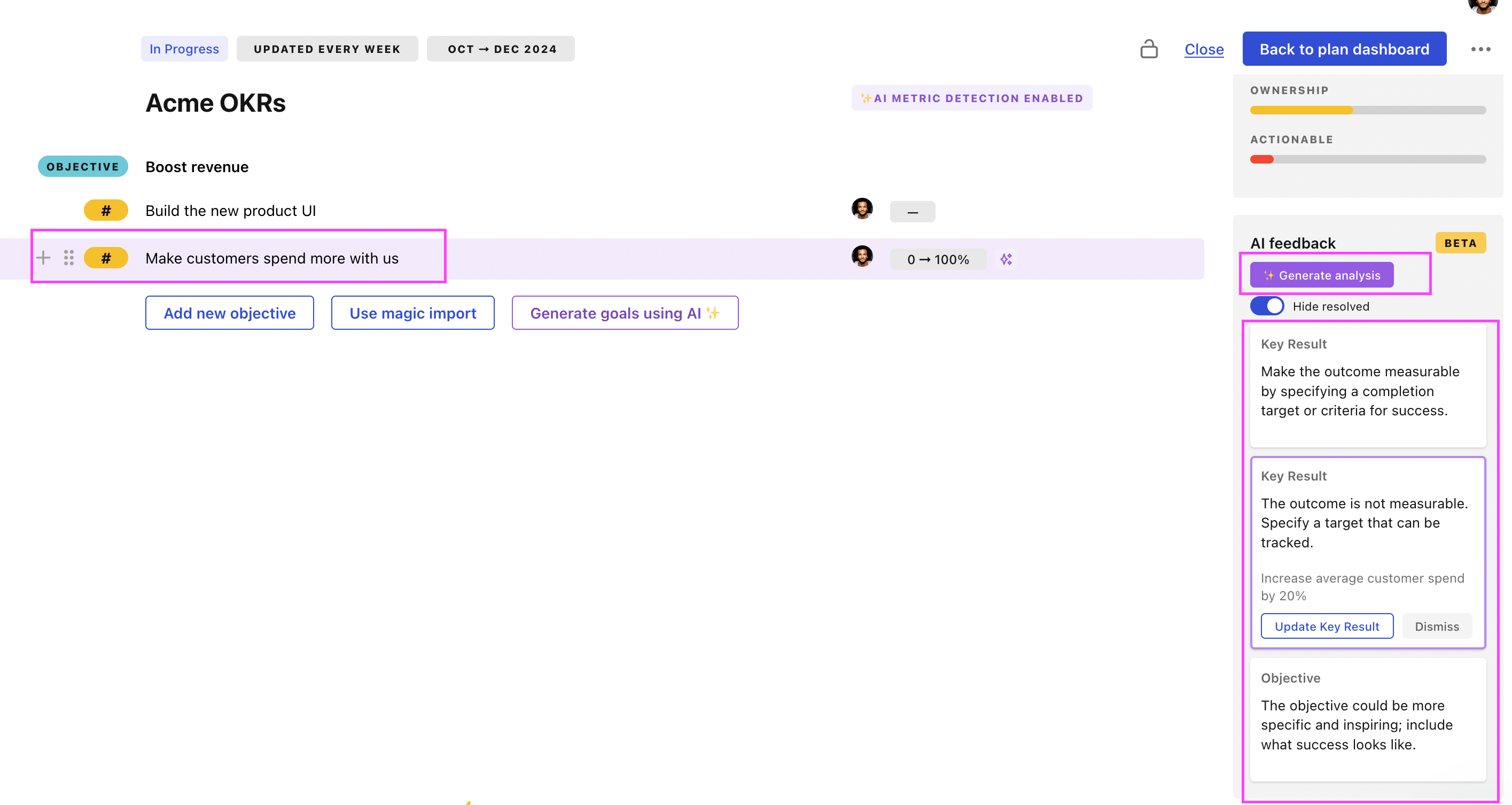
Use Tability feedback to improve existing OKRs
You can also use Tability's AI feedback to improve your OKRs if you already have existing goals. Just import them to the platform and click on the Generate analysis button.
Tability will scan your OKRs and offer different suggestions to improve them. This can range from a small rewrite of a statement to make it clearer to a complete rewrite of the entire OKR.