Security team OKR templates help teams align incident readiness, remediation work, and control improvements around outcomes the business can understand.
Choose a few measurable security outcomes for the quarter, then run consistent reviews so leadership can see where control or incident-response risk is building.
This page shows the top 10 of 24 templates for security team, with internal links to related categories and guidance for adapting the examples to your team.
Last template update in this category: 2025-03-20What this category is for
- Security Team planning for teams that need clearer priorities.
- Security Team execution tied to measurable business outcomes.
- Security Team reviews that keep progress visible each week.
Best outcomes to track
- Security Team goals connected to company-level execution.
- Faster identification of blockers and delivery risks.
- Stronger weekly accountability around measurable progress.
Related categories
Use these linked categories to explore adjacent planning areas and strengthen the internal topic cluster around security team.
Security Team OKR examples and templates
Start with these top 10 examples from 24 total templates in this category, then adapt the metrics and initiatives to fit your team's constraints and operating cadence.
OKRs to ensure full ISSO compliance through regular audits and security training
ObjectiveEnsure full ISSO compliance through regular audits and security training
KRTrain all new employees about ISSO compliance within their first week of employment
Schedule ISSO compliance training for new hires
Prepare relevant ISSO compliance materials
Conduct compliance training within their first week
KRIncrease the frequency of conducting audits to 100% every week from next quarter
Establish weekly audit schedule for consistent implementation
Monitor and track weekly audit outcomes constantly
Train audit team on the new weekly audit frequency
KRReduce security breaches by 90% through enhanced information security measures this quarter
Implement two-factor authentication for all system logins
Conduct regular cybersecurity training for staff
Update and strengthen all passwords regularly
OKRs to enhance security and compliance across end-user devices
ObjectiveEnhance security and compliance across end-user devices
KRTrain 85% of users in secure and compliant device usage practices
Regularly monitor and record user participation rates
Launch the training program for all users
Develop a comprehensive secure device usage training program
KRImplement multi-factor authentication on 90% of end-user devices
Assess current security measures on all end-user devices
Install and activate the identified software on 90% of devices
Identify software for multi-factor authentication implementation
KRMaintain 95% compliance rate on all end-user devices through regular audits
Identify non-compliant devices for immediate action
Regularly schedule and perform device compliance audits
Review and adjust compliance policies as necessary
OKRs to develop a Security Officer Performance Appraisal Plan for an Irish client
ObjectiveDevelop a Security Officer Performance Appraisal Plan for an Irish client
KRFinalize and deliver complete appraisal plan with client’s full approval
Deliver finalized appraisal plan to client
Review and finalize appraisal plan details
Obtain full client approval on plan
KRIdentify and define 10 performance metrics relevant to security work by week 3
Draft definitions for ten relevant metrics
Finalize and document identified metrics
Research existing security performance metrics
KRHold a minimum of 2 feedback sessions with customer for plan refinement
Arrange second session for revising plans based on feedback
Prepare detailed plan for feedback discussion
Schedule initial feedback session with customer
OKRs to increase security architecture review visibility at the program level
ObjectiveIncrease security architecture review visibility at the program level
KRImplement a dashboard presenting real-time security architecture review results
Test and launch the security architecture dashboard
Design an easy-to-read, real-time dashboard
Identify key metrics for the security architecture review
KROrganize monthly training sessions for all teams on interpreting security reviews
Identify topics and structure for security review training sessions
Send out communications about training sessions to all teams
Coordinate scheduling of speakers or trainers
KREstablish a weekly report system on security review outcomes across all programs
Schedule and supervise regular weekly reporting
Design a template for weekly security reports
Identify key metrics for security review outcomes
OKRs to enhance effectiveness of response processes for security incidents
ObjectiveEnhance effectiveness of response processes for security incidents
KRReduce average incident response time by 30%
Implement automated incident response software
Review and streamline incident report process
Enhance training of response team
KRConduct simulation exercises post-training to achieve at least 80% success rate
Monitor and measure success rates, aiming for 80% achievement
Implement simulation exercises regularly for all trained individuals
Develop a variety of simulation exercises relevant to the training content
KRImplement incident response training for 100% of the security team
Identify key incident response topics for comprehensive training
Develop interactive, practical training modules for the team
Schedule and conduct training sessions regularly
OKRs to streamline event egress to cut down by 8 seconds
ObjectiveStreamline event egress to cut down by 8 seconds
KRImplement efficient egress layout to enhance flow, reducing time by 3 seconds
Implement and test the newly proposed egress layout
Design new egress plan focusing on efficiency
Evaluate current egress layout for potential speed improvements
KRTrain event staff on rapid egress procedures, targeting 2 seconds reduction
Schedule regular egress drills for hands-on practice
Create detailed egress procedures for event staff training
Analyze drill results to identify improvement areas
KRIntroduce signages for smoother navigation, aiming at 3 seconds time decrease
Install new signage and monitor effectiveness in reducing navigation time
Identify key areas where signage is needed for improved navigation
Design clear, easy-to-understand signs for each identified area
OKRs to enhance production security for optimal operation efficiency
ObjectiveEnhance production security for optimal operation efficiency
KRImplement a secure authentication system reducing security breaches by 30%
Implement multi-factor authentication across all platforms
Regularly update and test password encryption methods
Conduct staff training on secure password practices
KRConduct weekly vulnerability audits and reduce identified risks by 50%
Analyze audit results to identify potential risks
Schedule weekly vulnerability audits for technical systems
Implement measures to mitigate identified risks by 50%
KRTrain 90% of staff on updated security protocols and practices
Identify staff members who need security training
Monitor and record staff training progress
Schedule periodic training sessions
OKRs to integrate security controls into development sprints
ObjectiveIntegrate security controls into development sprints
KRSuccessfully incorporate security controls into two sprints by end of Week 6
Implement security controls into sprints in Weeks 4-6
Develop detailed security control integration plans by Week 3
Identify security control requirements for both sprints in Week 1
KRFully train the team on security control integration by end of Week 3
Provide comprehensive learning materials and resources for the team
Evaluate team members' comprehensive understanding by end of Week 3
Schedule mandatory team training sessions on security control integration
KRAchieve a decrease in security incidents by 40% by end of Week 9
Implement a comprehensive cybersecurity training program for all employees
Foster a company-wide culture of security vigilance
Upgrade existing security infrastructure and software
OKRs to enhance proactive investigation through expanded log analysis
ObjectiveEnhance proactive investigation through expanded log analysis
KRLower the average response time to identified threats by 20%
Seek professional consultation on response strategy
Implement advanced threat detection software
Train staff to swiftly respond to threats
KRTrain the team on the new tool to improve threat identification by 40%
Organize a comprehensive training session on the new tool
Measure improvements in threat identification post-training
Select team members to participate in threat identification training
KRImplement advance log analysis tool to automatically identify and flag potential threats
Research and select an advanced log analysis tool
Train IT team on threat identification and response
Install and configure the chosen tool
OKRs to improve AI security requirements operationalization for developers’ comprehension
ObjectiveImprove AI security requirements operationalization for developers’ comprehension
KRDevelop and deploy a standardized AI security guideline by 25%
Draft a comprehensive AI security guideline
Reduce guideline by 25% focusing on core elements
Implement the streamlined AI security guideline across all systems
KRReduce misunderstandings in AI security requirements by 30% through improved documentation
Conduct regular staff trainings highlighting documentation procedures
Establish clear, concise writing guidelines for technical content
Implement a standardized format for all AI security requirement documents
KRConduct bi-weekly developer trainings on new AI security protocols resulting in 80% adherence
How to use Security Team OKRs well
Strong OKRs keep the team focused on measurable outcomes instead of a long task list. That means picking a clear objective, limiting the number of competing priorities, and reviewing progress every week.
Choose a few measurable security outcomes for the quarter, then run consistent reviews so leadership can see where control or incident-response risk is building.
Choosing software to run these OKRs?
Many teams looking for security team OKR examples are also comparing tools to roll them out. If you want to move from examples to execution, review our OKR software comparison guide to compare the best OKR software before you commit to a platform.
Related OKR template categories
If you are building a broader plan, these related categories can help you connect security team work to adjacent company priorities.
More OKR templates to explore
OKRs to enhance Safety Layout Design and Processes - Level 4
OKRs to minimize incidents to a maximum of six minor ones
OKRs to achieve zero loss time accidents
OKRs to enhance brand reputation to drive B2B lead generation
OKRs to amplify brand reputation to boost lead generation
OKRs to grow the user base via organic mobile acquisition
Not seeing what you need?
Use Tability AI to generate OKRs based on a prompt
Tability allows you to describe your goals in a prompt, and generate a fully editable OKR template in seconds.
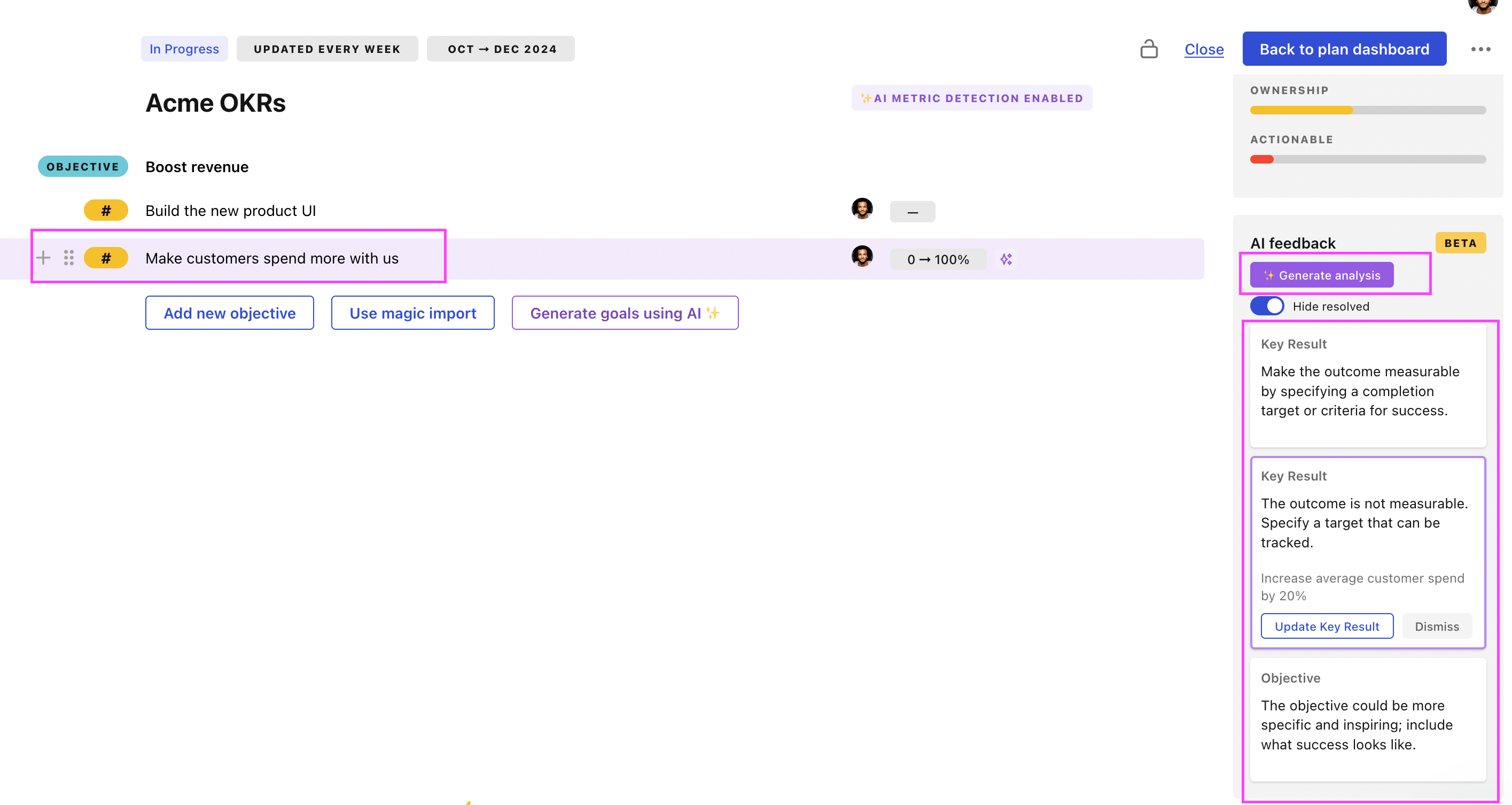
Use Tability feedback to improve existing OKRs
You can also use Tability's AI feedback to improve your OKRs if you already have existing goals. Just import them to the platform and click on the Generate analysis button.
Tability will scan your OKRs and offer different suggestions to improve them. This can range from a small rewrite of a statement to make it clearer to a complete rewrite of the entire OKR.