Security analyst OKR templates give practitioners a clearer way to show impact in detection, response, and remediation work. They are especially useful when teams want to make security execution easier to measure.
Define OKRs around measurable response and remediation outcomes rather than simply tracking case volume or raw activity.
This page shows the top 10 of 13 templates for security analysts, with internal links to related categories and guidance for adapting the examples to your team.
Last template update in this category: 2024-09-03What this category is for
- Security Analysts planning for teams that need clearer priorities.
- Security Analysts execution tied to measurable business outcomes.
- Security Analysts reviews that keep progress visible each week.
Best outcomes to track
- Security Analysts goals connected to company-level execution.
- Faster identification of blockers and delivery risks.
- Stronger weekly accountability around measurable progress.
Related categories
Use these linked categories to explore adjacent planning areas and strengthen the internal topic cluster around security analysts.
Security Analysts OKR examples and templates
Start with these top 10 examples from 13 total templates in this category, then adapt the metrics and initiatives to fit your team's constraints and operating cadence.
OKRs to enhance production security for optimal operation efficiency
ObjectiveEnhance production security for optimal operation efficiency
KRImplement a secure authentication system reducing security breaches by 30%
Implement multi-factor authentication across all platforms
Regularly update and test password encryption methods
Conduct staff training on secure password practices
KRConduct weekly vulnerability audits and reduce identified risks by 50%
Analyze audit results to identify potential risks
Schedule weekly vulnerability audits for technical systems
Implement measures to mitigate identified risks by 50%
KRTrain 90% of staff on updated security protocols and practices
Identify staff members who need security training
Monitor and record staff training progress
Schedule periodic training sessions
OKRs to strengthen SOC effectiveness to increase security operations productivity
ObjectiveStrengthen SOC effectiveness to increase security operations productivity
KRReduce false positive alarms from SOC by 30%
Improve analyst training for accurate threat prediction
Regularly update and fine-tune security system settings
Implement advanced anomaly detection algorithms
KRIncrease identification of real threats by 20%
Implement advanced threat detection systems
Conduct regular security awareness training
Strengthen information sharing with allies
KRImprove SOC response time to threats by 15%
Conduct regular response time drills for SOC team
Implement automated threat detection tools for quicker identification
Prioritize high-impact threats for immediate response
OKRs to improve Security Operation Centre Incident Response
ObjectiveImprove Security Operation Centre Incident Response
KRReduce average incident response time by 15%
Deploy automated incident detection and response tools
Train team on efficient incident management practices
Regularly conduct response time drills
KRIncrease team's cyber security certification levels by 30%
Plan and allocate budget for necessary certification exams and trainings
Identify current cybersecurity certification levels of all team members
Enroll team in targeted cybersecurity training programs
KRImplement new incident tracking software with 100% team adoption
Train team on new software usage
Evaluate and select suitable incident tracking software
Monitor and ensure full team adoption
OKRs to improve AI security requirements operationalization for developers’ comprehension
ObjectiveImprove AI security requirements operationalization for developers’ comprehension
KRDevelop and deploy a standardized AI security guideline by 25%
Draft a comprehensive AI security guideline
Reduce guideline by 25% focusing on core elements
Implement the streamlined AI security guideline across all systems
KRReduce misunderstandings in AI security requirements by 30% through improved documentation
Conduct regular staff trainings highlighting documentation procedures
Establish clear, concise writing guidelines for technical content
Implement a standardized format for all AI security requirement documents
KRConduct bi-weekly developer trainings on new AI security protocols resulting in 80% adherence
OKRs to establish robust security controls for DHS/ATO and NATO contracts
ObjectiveEstablish robust security controls for DHS/ATO and NATO contracts
KRConduct quarterly maintenance on all the security controls and document findings
Document observations and any maintenance executed
Review all security control systems thoroughly
Perform necessary maintenance on security controls
KRImplement 5 new security measures aligned with DHS/ATO requirements by a 100%
Identify potential security measures that align with DHS/ATO requirements
Implement and test the newly identified security measures
Review existing security measures for any DHS/ATO non-compliance
KRAchieve zero security breaches related to the NATO contracts information
Implement strong encryption on all NATO-related digital communication
Train staff in counter-intelligence and data protection practices
Regularly perform rigorous security audits and fix vulnerabilities
OKRs to bolster Protection Against P1 Issues
ObjectiveBolster Protection Against P1 Issues
KRImprove first-time resolution rate for P1 issues to 70% across all teams
Train agents on P1 issue recognition and resolution
Implement P1 issue escalation protocol
Regularly review P1 resolution analytics
KRImplement a 25% reduction in P1 issues through improved security protocols
Train staff in improved security protocols
Identify vulnerabilities in current security protocols
Develop improved, stringent security measures
KRAchieve 90% staff training completion on new security measures by quarter end
Monitor and report staff training progress regularly
Schedule mandatory training sessions for all staff
Develop comprehensive security training program
OKRs to successfully migrate all applications to a secure DevOps pipeline
ObjectiveSuccessfully migrate all applications to a secure DevOps pipeline
KRAchieve zero security incidents post-migration in the reviewed applications
Regularly review and update security measures
Implement solid security mechanisms post-migration
Conduct thorough security checks and audits before migration
KRTrain 80% of development team on secure DevOps pipeline management
Identify team members needing secure DevOps pipeline training
Organize a training program with a competent instructor
Schedule and implement training sessions for identified members
KRImplement secure DevOps pipeline framework for 50% of existing applications
Develop or acquire the necessary secure DevOps pipeline framework
Identify applications suitable for secure DevOps pipeline implementation
Roll out the framework across the identified applications
OKRs to minimize fraudulent transactions on debit cards
ObjectiveMinimize fraudulent transactions on debit cards
KRImplement two-factor authentication for 95% of online debit card transactions
Apply protocols to identified transactions
Identify debit card transactions without two-factor authentication
Develop user-friendly two-factor authentication protocols
KREducate 80% of users on secure practices in debit card usage
Implement a targeted educational email campaign
Develop informative content on secure debit card usage
Organize interactive webinars on secure card practices
KRReduce debit card fraud cases by 30% through upgraded security features
Regularly update anti-fraud software systems
Implement two-factor authentication for all debit card transactions
Incorporate biometric verification features into debit cards
OKRs to become a computer security expert
ObjectiveBecome a computer security expert
KRSuccessfully pass the Certified Ethical Hacker (CEH) exam with a score of 80% or higher
KRDevelop and execute a comprehensive security project, receiving positive feedback from industry experts
Collaborate with industry experts to gather insights and recommendations for improving security measures
Regularly monitor and evaluate the effectiveness of implemented security measures to ensure ongoing protection
Develop and implement robust security protocols and controls across all systems and processes
Conduct a thorough assessment of current security vulnerabilities and risks
KRComplete at least two online courses on computer security, scoring above 90% in each
Ensure mastery of course materials and aim to score above 90% in assessments
Devote dedicated hours per week to studying and completing the online courses
Research and identify two reputable online courses for computer security
Enroll in the selected online courses on computer security
KRImplement and manage effective security measures on personal computer resulting in zero malware incidents
Install a reliable antivirus software program on the personal computer
Enable automatic software updates for the operating system and all installed applications
Avoid clicking on suspicious links or downloading files from untrustworthy sources
Regularly update the antivirus software to ensure the latest protection against malware
OKRs to strengthen network security through enhanced logging capabilities
ObjectiveStrengthen network security through enhanced logging capabilities
KRImplement centralized logging infrastructure to capture and store network activity data
Regularly monitor and maintain the centralized logging infrastructure to ensure uninterrupted data capture
Assess existing network infrastructure to identify suitable centralized logging solutions
Configure the centralized logging infrastructure to collect and store the network activity data
Determine the appropriate tools and technologies required for capturing network activity data
KRIncrease network security by configuring an intrusion detection system (IDS) with real-time monitoring capabilities
KRImprove incident response effectiveness by integrating logging data with a security information and event management (SIEM) system
Regularly review and fine-tune the integration and alerting processes to optimize incident response
Analyze current logging data sources and identify gaps for integration with the SIEM system
Develop standardized alerting rules within the SIEM system based on integrated logging data
Configure the SIEM system to ingest and aggregate logging data from all relevant sources
KRIdentify and resolve security vulnerabilities by regularly reviewing and analyzing network log data
Set up a regular schedule for reviewing and analyzing network log data
Generate reports based on network log data analysis to prioritize and address vulnerabilities
Implement necessary measures to resolve identified security vulnerabilities promptly and effectively
Use security software to identify and monitor potential security vulnerabilities
How to use Security Analysts OKRs well
Strong OKRs keep the team focused on measurable outcomes instead of a long task list. That means picking a clear objective, limiting the number of competing priorities, and reviewing progress every week.
Define OKRs around measurable response and remediation outcomes rather than simply tracking case volume or raw activity.
Choosing software to run these OKRs?
Many teams looking for security analysts OKR examples are also comparing tools to roll them out. If you want to move from examples to execution, review our OKR software comparison guide to compare the best OKR software before you commit to a platform.
Related OKR template categories
If you are building a broader plan, these related categories can help you connect security analysts work to adjacent company priorities.
More OKR templates to explore
OKRs to streamline Inbound Procedures for Warehouse Efficiency
OKRs to boost overall employee happiness levels
OKRs to establish solid groundwork for expansion into new markets
OKRs to boost annual sales figures by 15%
OKRs to ensure financial efficiency at Wonderfly Arena
OKRs to ensure cost-efficiency at Wonderfly Arena
Not seeing what you need?
Use Tability AI to generate OKRs based on a prompt
Tability allows you to describe your goals in a prompt, and generate a fully editable OKR template in seconds.
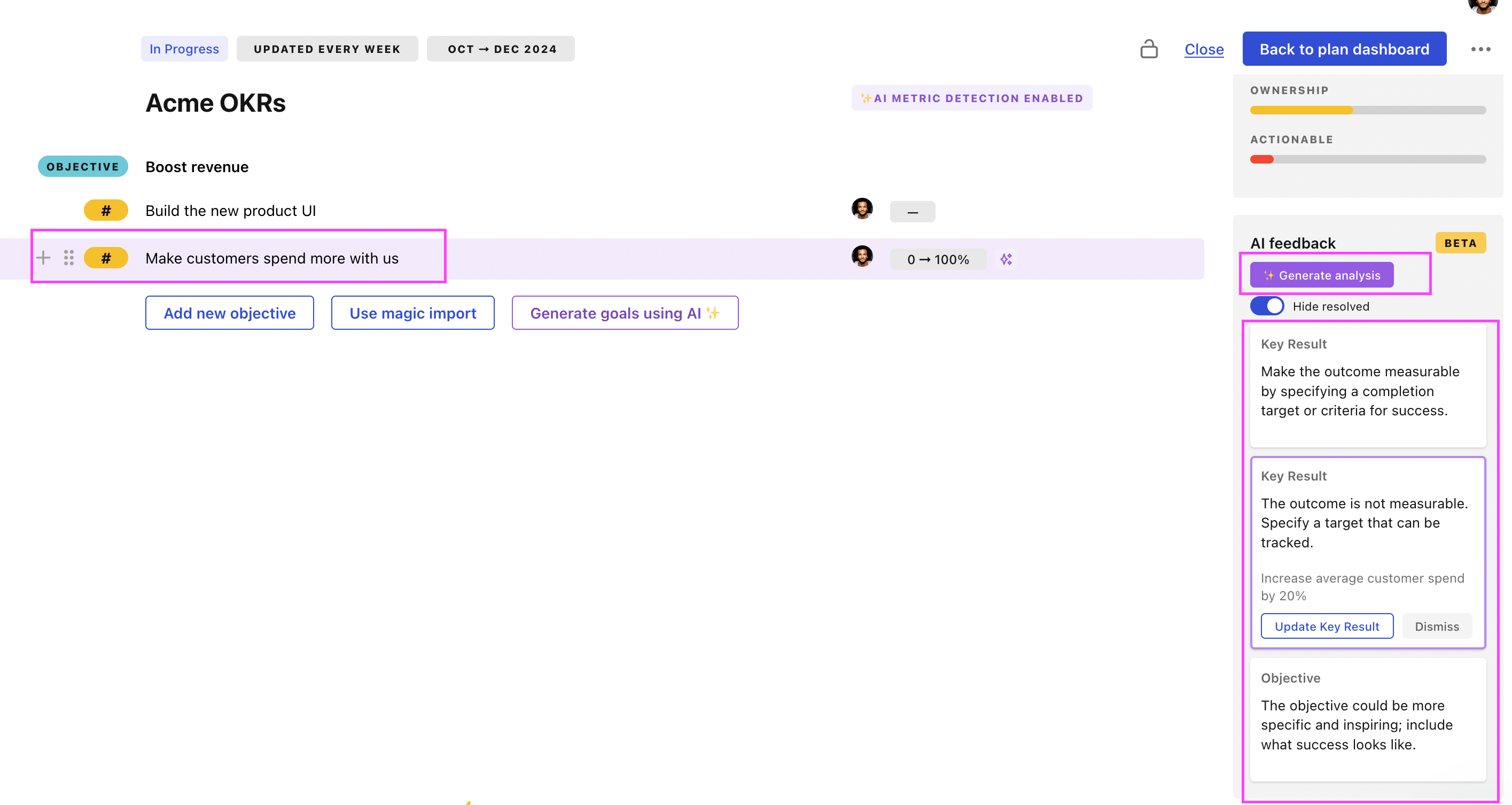
Use Tability feedback to improve existing OKRs
You can also use Tability's AI feedback to improve your OKRs if you already have existing goals. Just import them to the platform and click on the Generate analysis button.
Tability will scan your OKRs and offer different suggestions to improve them. This can range from a small rewrite of a statement to make it clearer to a complete rewrite of the entire OKR.