These Security Manager OKR templates are meant to help teams move from ideas and projects to measurable business outcomes. Use them as a starting point, then tailor the metrics and initiatives to the reality of your company.
Use Security Manager OKRs to define what success looks like this quarter, then track them weekly so the team can quickly spot blockers, learn, and adjust execution.
This page shows the top 6 of 6 templates for security manager, with internal links to related categories and guidance for adapting the examples to your team.
Last template update in this category: 2024-09-05What this category is for
- Teams that need a clearer operating rhythm for security manager work.
- Managers who want examples they can adapt into outcome-focused quarterly plans.
- Leaders comparing adjacent categories before choosing the best OKR direction.
Best outcomes to track
- Security Manager priorities tied to measurable business outcomes.
- Weekly check-ins that surface blockers before they become delivery issues.
- Better alignment between initiatives and the metrics that matter.
Related categories
Use these linked categories to explore adjacent planning areas and strengthen the internal topic cluster around security manager.
Security Manager OKR examples and templates
Start with these top 6 examples from 6 total templates in this category, then adapt the metrics and initiatives to fit your team's constraints and operating cadence.
OKRs to streamline event egress to cut down by 8 seconds
ObjectiveStreamline event egress to cut down by 8 seconds
KRImplement efficient egress layout to enhance flow, reducing time by 3 seconds
Implement and test the newly proposed egress layout
Design new egress plan focusing on efficiency
Evaluate current egress layout for potential speed improvements
KRTrain event staff on rapid egress procedures, targeting 2 seconds reduction
Schedule regular egress drills for hands-on practice
Create detailed egress procedures for event staff training
Analyze drill results to identify improvement areas
KRIntroduce signages for smoother navigation, aiming at 3 seconds time decrease
Install new signage and monitor effectiveness in reducing navigation time
Identify key areas where signage is needed for improved navigation
Design clear, easy-to-understand signs for each identified area
OKRs to strengthen SOC effectiveness to increase security operations productivity
ObjectiveStrengthen SOC effectiveness to increase security operations productivity
KRReduce false positive alarms from SOC by 30%
Improve analyst training for accurate threat prediction
Regularly update and fine-tune security system settings
Implement advanced anomaly detection algorithms
KRIncrease identification of real threats by 20%
Implement advanced threat detection systems
Conduct regular security awareness training
Strengthen information sharing with allies
KRImprove SOC response time to threats by 15%
Conduct regular response time drills for SOC team
Implement automated threat detection tools for quicker identification
Prioritize high-impact threats for immediate response
OKRs to upgrade and streamline physical security operations
ObjectiveUpgrade and streamline physical security operations
KRIncrease security coverage by 20% through additional surveillance systems
Investigate current surveillance system capabilities and limitations
Implement new surveillance systems accordingly
Research and identify potential additional surveillance technology
KRDecrease response times to security incidents by 25%
KRImplement a digital security management system with 100% staff training completion
Track and achieve 100% training completion
Choose a comprehensive digital security management system
Develop an all-staff training curriculum for the system
OKRs to enhance overall system access management
ObjectiveEnhance overall system access management
KRImplement two-factor authentication for 80% of users
Determine necessary resources for two-factor authentication implementation
Develop an implementation strategy focusing on 80% user coverage
Communicate these changes and provide user support for transition
KRDecrease unauthorized access attempts by 50%
Implement two-factor authentication for all system logins
Run frequent security training sessions for employees
Regularly update and strengthen password policies
KRTrain 90% of staff on new access management procedures
Identify employees needing training in access management procedures
Implement and monitor progress of training sessions
Coordinate with HR to schedule mandatory procedure training sessions
OKRs to improve Identity Access Management for large scale clients
ObjectiveImprove Identity Access Management for large scale clients
KRReduce access credential errors by 20%
Introduce regular password update reminders for employees
Implement a comprehensive access credential training program
Upgrade access security software to reduce login errors
KRImplement two-factor authentication for 90% of big customers
Deploy system to selected clients
Develop and test two-factor authentication system
Identify 90% of biggest clients requiring two-factor authentication
KRIncrease security incident response speed by 30%
Train staff in faster threat identification procedures
Implement automated threat detection and response tools
Streamline incident reporting and escalation processes
OKRs to improve website security through effective deployment of content security policy
ObjectiveImprove website security through effective deployment of content security policy
KRReduce the number of security breaches and incidents related to content vulnerabilities
Develop and implement comprehensive content security policies and guidelines
Regularly update and patch content management systems and software to mitigate security risks
Provide ongoing training and awareness programs to educate employees about content vulnerabilities
Conduct regular security audits to identify and address content vulnerabilities
KRIncrease overall security rating of the website as measured by independent security auditing tools
Implement SSL/TLS certificates to enable secure HTTPS communication for the website
Conduct penetration tests to identify and fix potential weak points in the website's security
Implement strong and unique passwords, two-factor authentication, and regular user access reviews
Regularly update and patch all software and plugins to address known vulnerabilities
KRImplement and activate content security policy across all website pages
Define and document the content security policy guidelines and restrictions
Conduct a thorough website audit to identify potential security vulnerabilities
Test and validate the implemented content security policy for effectiveness and accuracy
Modify website code to include the content security policy header on all pages
KREnhance user experience by minimizing false positive alerts from the content security policy
Implement machine learning algorithms to optimize content security policy detection
Analyze log data to identify patterns and fine-tune alert triggers
Review and update content security policy rules for better accuracy
Collaborate with developers to eliminate false positives through code improvements
How to use Security Manager OKRs well
Strong OKRs keep the team focused on measurable outcomes instead of a long task list. That means picking a clear objective, limiting the number of competing priorities, and reviewing progress every week.
Use Security Manager OKRs to define what success looks like this quarter, then track them weekly so the team can quickly spot blockers, learn, and adjust execution.
Choosing software to run these OKRs?
Many teams looking for security manager OKR examples are also comparing tools to roll them out. If you want to move from examples to execution, review our OKR software comparison guide to compare the best OKR software before you commit to a platform.
Related OKR template categories
If you are building a broader plan, these related categories can help you connect security manager work to adjacent company priorities.
- security team OKR templates
- security analyst OKR templates
- leadership OKR templates
- strategic planning OKR templates
- operations OKR templates
- operations team OKR templates
More OKR templates to explore
OKRs to build a Python tool for efficient tracing of community cohort members
OKRs to secure leadership in POS and online payment solutions market
OKRs to enhance productivity across all regional offices
OKRs to enhance region-wide cooperation to exceed customer satisfaction
OKRs to enhance cross-divisional resource collaboration in the region
OKRs to increase financial sustainability of our non-profit organisation
Not seeing what you need?
Use Tability AI to generate OKRs based on a prompt
Tability allows you to describe your goals in a prompt, and generate a fully editable OKR template in seconds.
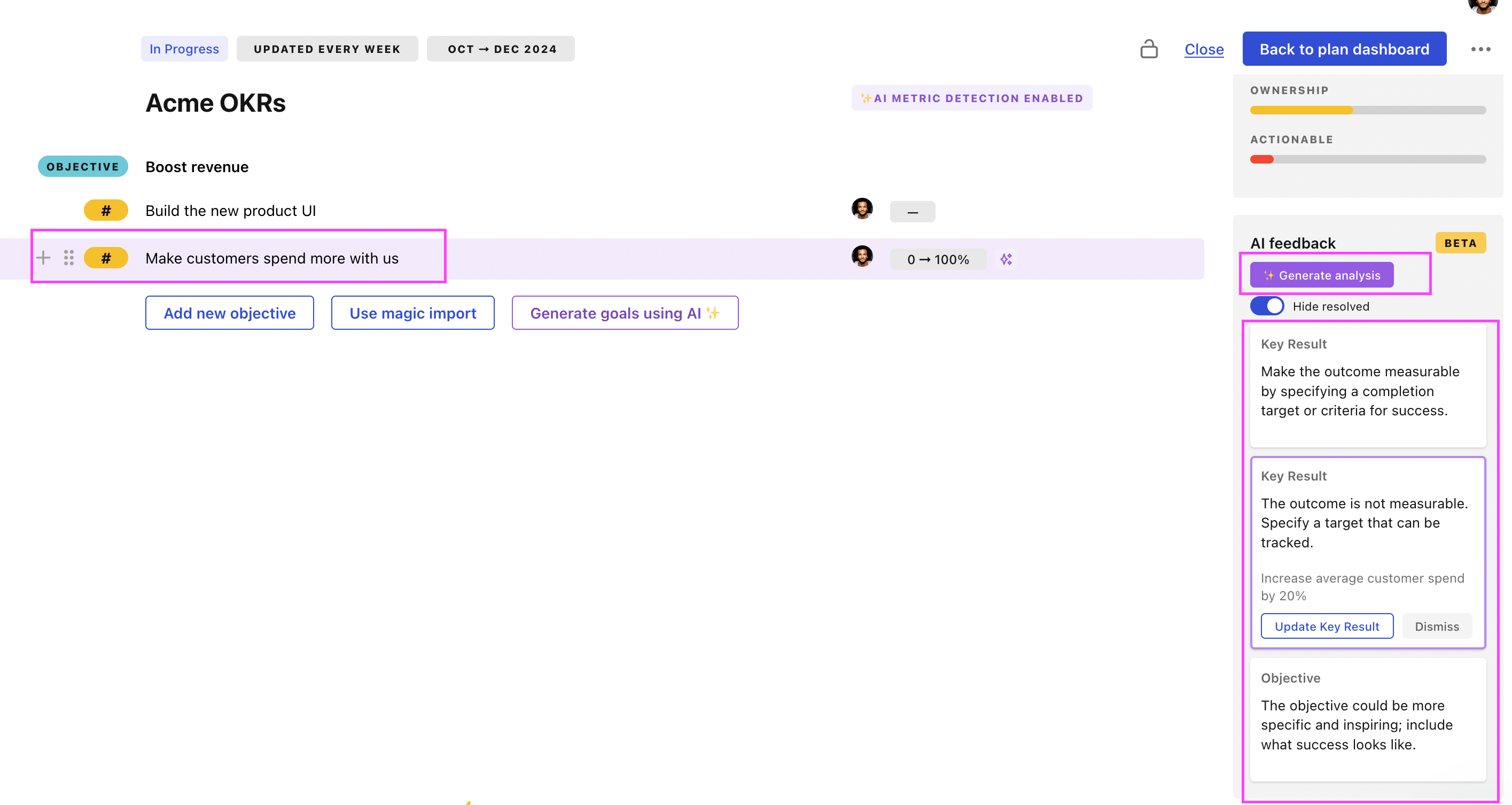
Use Tability feedback to improve existing OKRs
You can also use Tability's AI feedback to improve your OKRs if you already have existing goals. Just import them to the platform and click on the Generate analysis button.
Tability will scan your OKRs and offer different suggestions to improve them. This can range from a small rewrite of a statement to make it clearer to a complete rewrite of the entire OKR.