Security OKR templates help teams connect technical security work to business risk reduction. They are useful when security leaders need clearer ways to show progress, accountability, and resilience.
Set security OKRs around measurable changes in exposure, remediation, readiness, or control strength so the weekly review stays outcome-focused.
This page shows the top 4 of 4 templates for security, with internal links to related categories and guidance for adapting the examples to your team.
Last template update in this category: 2024-06-26What this category is for
- Security planning for teams that need clearer priorities.
- Security execution tied to measurable business outcomes.
- Security reviews that keep progress visible each week.
Best outcomes to track
- Security goals connected to company-level execution.
- Faster identification of blockers and delivery risks.
- Stronger weekly accountability around measurable progress.
Related categories
Use these linked categories to explore adjacent planning areas and strengthen the internal topic cluster around security.
Priority hubs
Security OKR examples and templates
Start with these top 4 examples from 4 total templates in this category, then adapt the metrics and initiatives to fit your team's constraints and operating cadence.
OKRs to enhance the organization's information technology efficiency and security
ObjectiveEnhance the organization's information technology efficiency and security
KRIncrease IT systems uptime to 99.9% across all operations
Introduce proactive system performance monitoring
Regularly update and patch all software systems
Implement robust and diverse backup servers for essential systems
KRImplement multi-factor authentication for 90% of users to enhance security
Guide users through the multi-factor adoption process
Choose a suitable multi-factor authentication system
Identify and classify users based on access levels and security requirements
KRDecrease system-related user complaints by 30% through proactive IT support improvements
Enhance technical troubleshooting protocols
Implement continuous monitoring for system performance
Develop comprehensive IT support training programs
OKRs to conduct regular penetration testing and code reviews
ObjectiveImprove security through regular penetration testing and code reviews
KREnsure all critical vulnerabilities found in penetration testing are remediated within 2 weeks
KRConduct code reviews for all new features and major changes before deployment
KRImplement at least 80% of code review recommendations within the next release cycle
KRIncrease the frequency of penetration testing from once a quarter to twice a month
OKRs to attain great security standards
ObjectiveAttain great security standards
KRAll developers score 90+ in our security awareness training
KR100% of devices are enrolled in a Mobile Device Management system
KR100% of our services have a threat mitigation system in place
KROur policies cover 100% of the ISO 27001 requirements
OKRs to increase security awareness
ObjectiveMake security part of our culture
KRRoll out fleet management pilot to 30% of the company
KR2FA is used on all 3rd party services used by employees
KR100% of our employees have gone through security training
How to use Security OKRs well
Strong OKRs keep the team focused on measurable outcomes instead of a long task list. That means picking a clear objective, limiting the number of competing priorities, and reviewing progress every week.
Set security OKRs around measurable changes in exposure, remediation, readiness, or control strength so the weekly review stays outcome-focused.
Choosing software to run these OKRs?
Many teams looking for security OKR examples are also comparing tools to roll them out. If you want to move from examples to execution, review our OKR software comparison guide to compare the best OKR software before you commit to a platform.
Related OKR template categories
If you are building a broader plan, these related categories can help you connect security work to adjacent company priorities.
More OKR templates to explore
OKRs to enhance risk management and business support systems
OKRs to enhance product suite experience for small businesses and accountants
OKRs to enhance the integration platform and developer environment
OKRs to boost employees' mastery in top five key competencies
OKRs to streamline competency development and retention for improved business performance
OKRs to accelerate workforce effectiveness through transformative performance management
Not seeing what you need?
Use Tability AI to generate OKRs based on a prompt
Tability allows you to describe your goals in a prompt, and generate a fully editable OKR template in seconds.
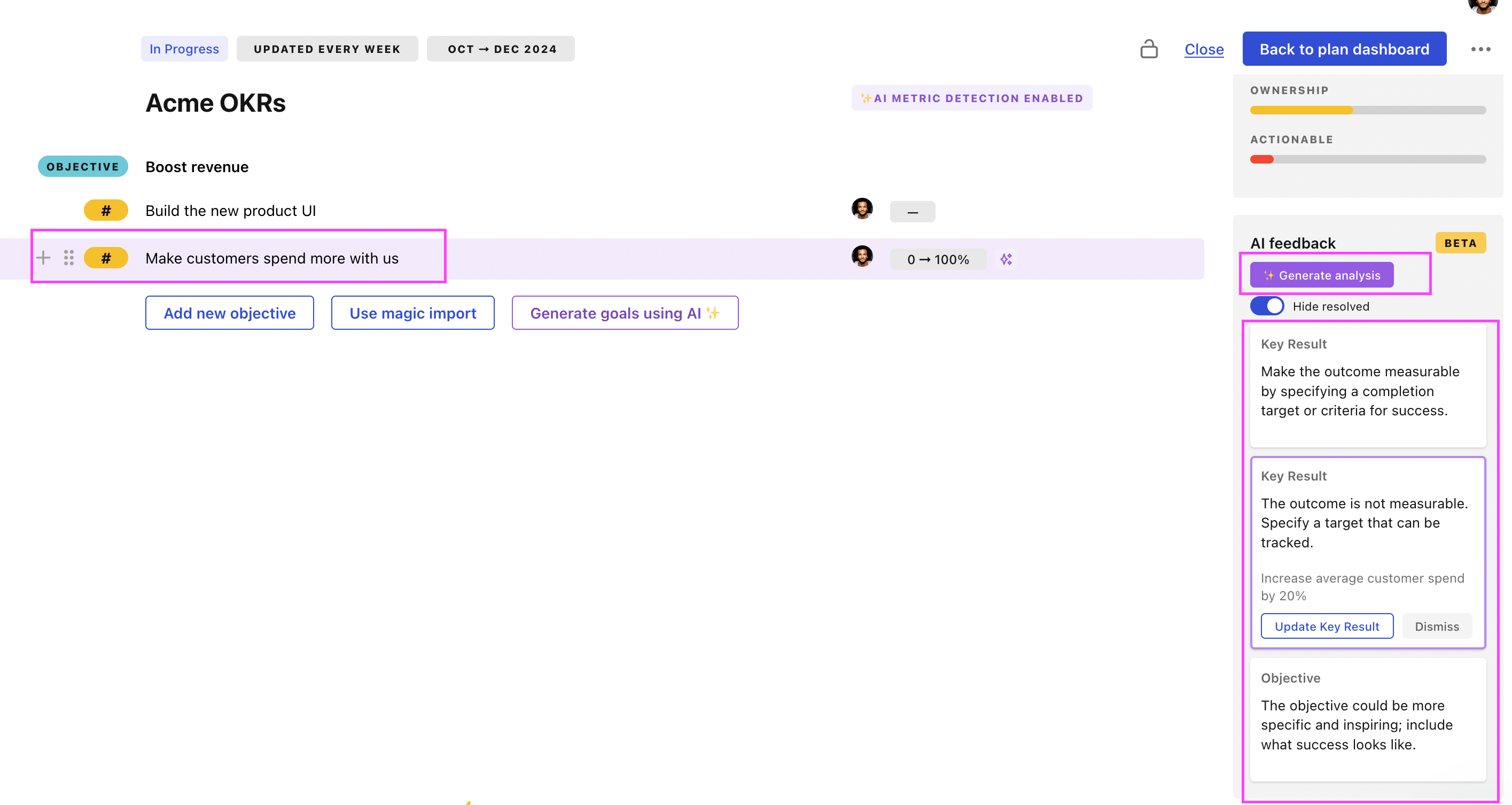
Use Tability feedback to improve existing OKRs
You can also use Tability's AI feedback to improve your OKRs if you already have existing goals. Just import them to the platform and click on the Generate analysis button.
Tability will scan your OKRs and offer different suggestions to improve them. This can range from a small rewrite of a statement to make it clearer to a complete rewrite of the entire OKR.