These Cybersecurity Team OKR templates are meant to help teams move from ideas and projects to measurable business outcomes. Use them as a starting point, then tailor the metrics and initiatives to the reality of your company.
Use Cybersecurity Team OKRs to define what success looks like this quarter, then track them weekly so the team can quickly spot blockers, learn, and adjust execution.
This page shows the top 8 of 8 templates for cybersecurity team, with internal links to related categories and guidance for adapting the examples to your team.
Last template update in this category: 2026-03-01What this category is for
- Teams that need a clearer operating rhythm for cybersecurity team work.
- Managers who want examples they can adapt into outcome-focused quarterly plans.
- Leaders comparing adjacent categories before choosing the best OKR direction.
Best outcomes to track
- Cybersecurity Team priorities tied to measurable business outcomes.
- Weekly check-ins that surface blockers before they become delivery issues.
- Better alignment between initiatives and the metrics that matter.
Related categories
Use these linked categories to explore adjacent planning areas and strengthen the internal topic cluster around cybersecurity team.
Cybersecurity Team OKR examples and templates
Start with these top 8 examples from 8 total templates in this category, then adapt the metrics and initiatives to fit your team's constraints and operating cadence.
OKRs to drive cybersecurity awareness across the organization
ObjectiveDrive cybersecurity awareness across the organization
KRImplement a cybersecurity newsletter reaching all staff members
Distribute the newsletter to all staff members
Create engaging content for the newsletter
Identify relevant cybersecurity topics for the newsletter
KRAchieve a 25% reduction in reported phishing attempts
Conduct regular staff cyber security training
Regularly update and patch all systems
Implement advanced email filtering software
KRHave 90% of employees complete a cybersecurity training course
Monitor and track course completion
Identify available cybersecurity training courses
Enroll employees in selected cybersecurity course
OKRs to enhance the effectiveness of the vulnerability management program
ObjectiveEnhance the effectiveness of the vulnerability management program
KRImplement updates to the vulnerability detection system by 25%
Plan and develop necessary system updates and enhancements
Execute implementation of updated system at 25% capacity
Assess current vulnerability detection system for potential improvements
KRConduct training sessions for 80% of the IT staff on improved vulnerability management practices
Schedule and conduct the training sessions
Create an advanced vulnerability management curriculum
Identify IT staff that require vulnerability management training
KRReduce the number of vulnerability incidents by 30%
Regularly train staff about online threats
Implement an updated, robust cybersecurity program
Run weekly system vulnerability checks
OKRs to streamline and enhance application defense runtime
ObjectiveStreamline and enhance application defense runtime
KRImprove application response time by at least 40%
Invest in higher-quality, faster server hardware
Identify and eliminate bottlenecks in the application's code
Optimize the application’s database queries
KRImplement patches for identified vulnerabilities in 85% of applications
Identify vulnerable applications requiring patch updates
Acquire and prepare necessary patches for applications
Successfully implement patches to 85% of identified applications
KRDevelop a checklist of top 5 defense runtime vulnerabilities to address
Draft and refine checklist based on the findings
Consult with cybersecurity experts to gain additional insights
Research common defense runtime vulnerabilities in recent cybersecurity literature
OKRs to strengthen overall cybersecurity infrastructure
ObjectiveStrengthen overall cybersecurity infrastructure
KRConduct and pass two simulated cyber attacks without major system compromise
Demonstrate successful defense in a post-simulation review
Prepare and execute two different simulated cyber attack scenarios
Evaluate and address vulnerabilities exposed from the simulations
KRTrain 95% of employees on latest cybersecurity best practices
Develop a comprehensive cybersecurity training module
Conduct a needs assessment for cybersecurity training
Schedule and implement the training sessions
KRImplement multifactor authentication for all system users by end of quarter
Identify systems and platforms needing multifactor authentication
Train all system users on new authentication protocol
Select and purchase multifactor authentication software
OKRs to establish unparalleled data leak protection solution
ObjectiveEstablish unparalleled data leak protection solution
KRIncrease client satisfaction regarding data security by 25% through feedback surveys
Analyze survey responses for areas of improvement
Develop and execute strategies to address identified issues
Implement consistent client feedback surveys on data security
KRDevelop and implement a cutting-edge encryption system by increasing R&D team by 15%
Execute full implementation of new encryption system
Identify talent to expand R&D team by an additional 15%
Develop advanced encryption system prototype
KRReduce successful cyber attacks on our system by 80%
Implement multi-factor authentication for all system users
Regularly update and patch system software
Conduct frequent cybersecurity training for employees
OKRs to enhance fraud detection and prevention in the payment system
ObjectiveEnhance fraud detection and prevention in the payment system
KRReduce the number of fraudulent transactions by 25% through enhanced system security
Invest in fraud detection and prevention software
Conduct regular cybersecurity audits and fixes
Implement advanced encryption techniques for payment transactions
KRImplement machine learning algorithms to increase fraud detection accuracy by 40%
Train the algorithms with historical fraud data
Select appropriate machine learning algorithms for fraud detection
Test and tweak models' accuracy to achieve a 40% increase
KRTrain staff on new security protocols to reduce manual errors by 30%
Monitor and evaluate reduction in manual errors post-training
Schedule mandatory training sessions for all staff
Develop comprehensive training on new security protocols
OKRs to embed security consciousness in business operations
ObjectiveEmbed security consciousness in business operations
KRReduce security breaches by 25% through rigorous employee training
Implement mandatory cybersecurity training for all employees
Schedule regular refresher courses on data protection
Update security policies and disseminate to staff
KREstablish a quarterly security audit to identify potential vulnerabilities
Schedule regular audits with a professional auditor
Define the scope of each quarterly security audit
Create a process to address identified vulnerabilities
KRAchieve 100% compliance on mandatory security awareness training by all employees
Organize regular training sessions for all personnel
Monitor and document each employee's training progress
Distribute security awareness training materials to all employees
OKRs to increase efficiency and scalability through cloud deployment
ObjectiveIncrease efficiency and scalability through cloud deployment
KREnhance data security by implementing robust cloud security protocols and achieving compliance certifications
Conduct a comprehensive review of current cloud security protocols and identify weaknesses
Regularly monitor and assess cloud security protocols and update as needed
Develop and implement an updated cloud security framework based on industry best practices
Ensure all necessary compliance certifications are achieved and regularly maintained
KRAchieve a minimum of 99.9% uptime by ensuring seamless integration and high availability in the cloud
KRImprove response time by optimizing cloud infrastructure to achieve 20% faster application performance
Analyze current cloud infrastructure to identify performance bottlenecks hindering application response time
Optimize code and queries by analyzing and improving inefficient code segments
Utilize content delivery network (CDN) for faster content delivery and reduced latency
Implement caching mechanisms to store frequently accessed data and minimize database calls
KRReduce infrastructure costs by migrating 80% of applications and services to the cloud
How to use Cybersecurity Team OKRs well
Strong OKRs keep the team focused on measurable outcomes instead of a long task list. That means picking a clear objective, limiting the number of competing priorities, and reviewing progress every week.
Use Cybersecurity Team OKRs to define what success looks like this quarter, then track them weekly so the team can quickly spot blockers, learn, and adjust execution.
Choosing software to run these OKRs?
Many teams looking for cybersecurity team OKR examples are also comparing tools to roll them out. If you want to move from examples to execution, review our OKR software comparison guide to compare the best OKR software before you commit to a platform.
Related OKR template categories
If you are building a broader plan, these related categories can help you connect cybersecurity team work to adjacent company priorities.
- leadership OKR templates
- strategic planning OKR templates
- operations OKR templates
- operations team OKR templates
- sales OKR templates
- sales team OKR templates
More OKR templates to explore
OKRs to minimize expenditure on application hosting
OKRs to drive an effective agile transformation for all team operations
OKRs to construct an interactive dashboard in Tableau
OKRs to enhance skills and competencies as a Scrum Master and Agile coach
OKRs to achieve MongoDB certification
OKRs to enhance our overall communication effectiveness
Not seeing what you need?
Use Tability AI to generate OKRs based on a prompt
Tability allows you to describe your goals in a prompt, and generate a fully editable OKR template in seconds.
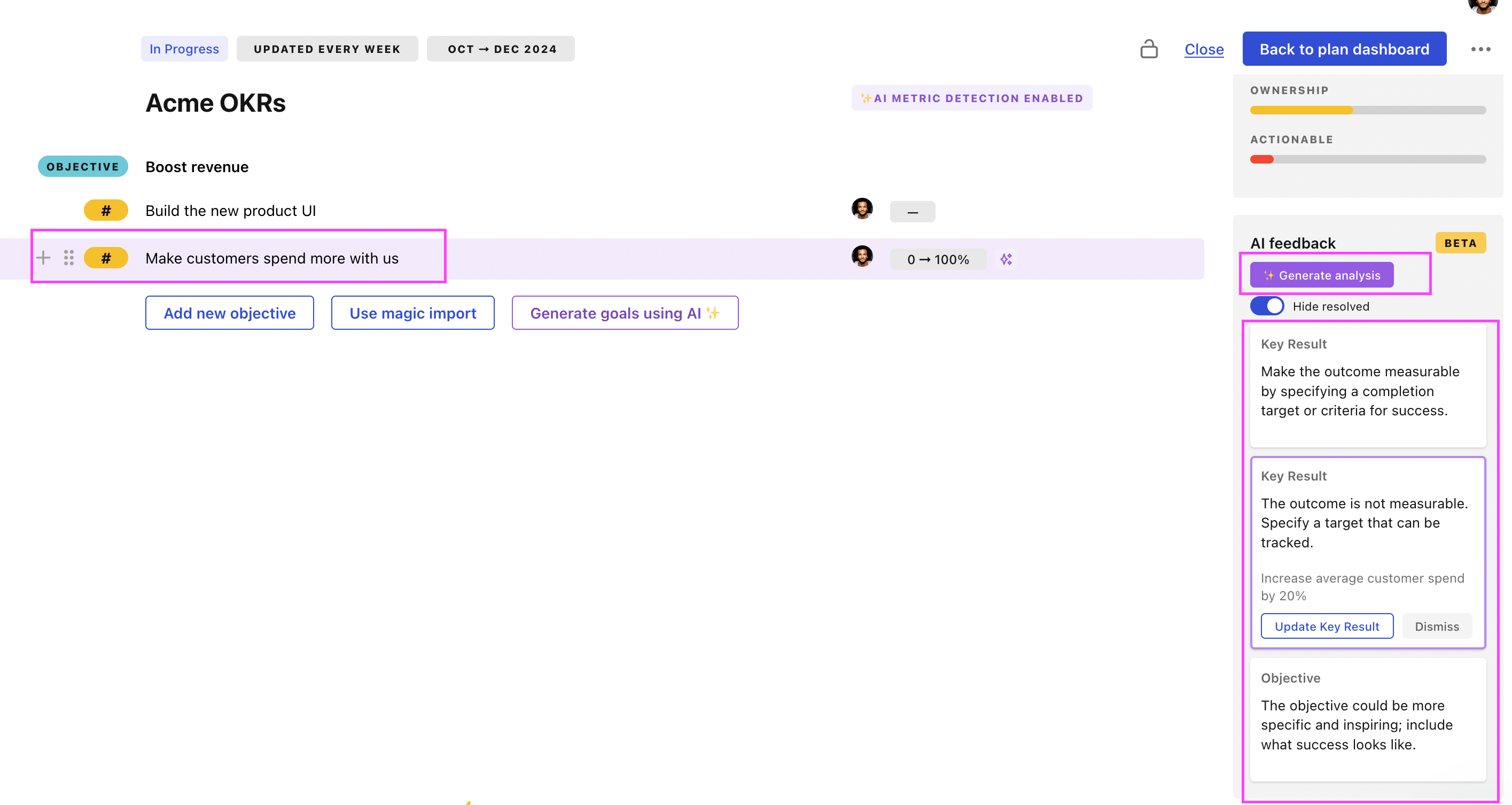
Use Tability feedback to improve existing OKRs
You can also use Tability's AI feedback to improve your OKRs if you already have existing goals. Just import them to the platform and click on the Generate analysis button.
Tability will scan your OKRs and offer different suggestions to improve them. This can range from a small rewrite of a statement to make it clearer to a complete rewrite of the entire OKR.