These System Security OKR templates are meant to help teams move from ideas and projects to measurable business outcomes. Use them as a starting point, then tailor the metrics and initiatives to the reality of your company.
Use System Security OKRs to define what success looks like this quarter, then track them weekly so the team can quickly spot blockers, learn, and adjust execution.
This page shows the top 1 of 1 template for system security, with internal links to related categories and guidance for adapting the examples to your team.
Last template update in this category: 2024-03-14What this category is for
- Teams that need a clearer operating rhythm for system security work.
- Managers who want examples they can adapt into outcome-focused quarterly plans.
- Leaders comparing adjacent categories before choosing the best OKR direction.
Best outcomes to track
- System Security priorities tied to measurable business outcomes.
- Weekly check-ins that surface blockers before they become delivery issues.
- Better alignment between initiatives and the metrics that matter.
Related categories
Use these linked categories to explore adjacent planning areas and strengthen the internal topic cluster around system security.
System Security OKR examples and templates
Start with these top 1 examples from 1 total template in this category, then adapt the metrics and initiatives to fit your team's constraints and operating cadence.
OKRs to enhance system security for robust protection
ObjectiveEnhance system security for robust protection
KRAchieve a 95% score in independent security audits validating system security protocols
Implement necessary updates and enhancements to address identified security gaps
Collaborate with external security experts to perform comprehensive security audits
Conduct thorough review of current security protocols and identify areas for improvement
Continuously monitor and evaluate system security measures to maintain a 95% audit score
KRReduce number of security breaches by 20% through enhanced authentication measures
Train employees on best practices for recognizing and avoiding phishing attacks
Implement two-factor authentication system for all users
Enhance password requirements and enforce regular password updates
Conduct regular security audits to identify vulnerabilities and address them promptly
KRImprove application vulnerability by reducing critical security issues by 15%
Train developers and staff on secure coding practices and security best practices
Implement regular security audits and vulnerability assessments on the application
Update and patch software and libraries regularly to address security vulnerabilities
Implement stricter access controls and enforce strong password policies for application access
KRIncrease employee awareness through mandatory security training with 100% completion rate
Enforce strict deadlines and reminders to ensure all employees complete the security training
Create an engaging and interactive security training program for all employees
Evaluate the effectiveness of the security training program by conducting regular assessments
Implement a digital platform for employees to easily access and complete security training
How to use System Security OKRs well
Strong OKRs keep the team focused on measurable outcomes instead of a long task list. That means picking a clear objective, limiting the number of competing priorities, and reviewing progress every week.
Use System Security OKRs to define what success looks like this quarter, then track them weekly so the team can quickly spot blockers, learn, and adjust execution.
Choosing software to run these OKRs?
Many teams looking for system security OKR examples are also comparing tools to roll them out. If you want to move from examples to execution, review our OKR software comparison guide to compare the best OKR software before you commit to a platform.
Related OKR template categories
If you are building a broader plan, these related categories can help you connect system security work to adjacent company priorities.
- leadership OKR templates
- strategic planning OKR templates
- operations OKR templates
- operations team OKR templates
- sales OKR templates
- sales team OKR templates
More OKR templates to explore
OKRs to cultivate an inclusive and engaging work environment for all employees
OKRs to seamlessly integrate values into community functions and relationships
OKRs to cultivate a resilient and enduring organizational culture
OKRs to minimize exposure to compliance and cybersecurity threats
OKRs to mitigate the risk associated with software maintenance
OKRs to improve system efficiency and dependability
Not seeing what you need?
Use Tability AI to generate OKRs based on a prompt
Tability allows you to describe your goals in a prompt, and generate a fully editable OKR template in seconds.
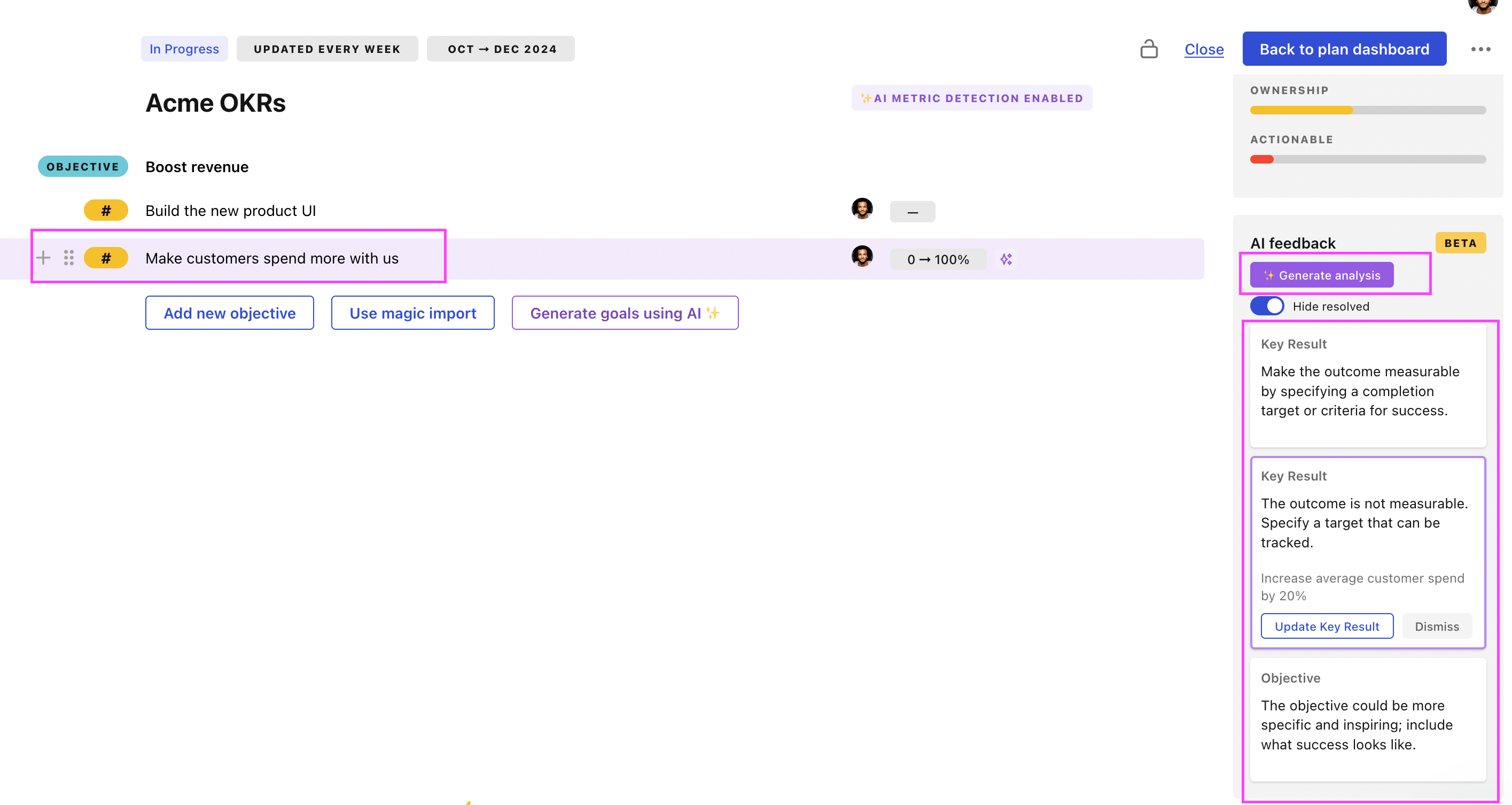
Use Tability feedback to improve existing OKRs
You can also use Tability's AI feedback to improve your OKRs if you already have existing goals. Just import them to the platform and click on the Generate analysis button.
Tability will scan your OKRs and offer different suggestions to improve them. This can range from a small rewrite of a statement to make it clearer to a complete rewrite of the entire OKR.