The strategy "Implementing AI Strategies for Cybersecurity Enhancement" focuses on leveraging artificial intelligence to improve various aspects of cybersecurity. It aims to enhance threat detection accuracy through machine learning models that analyze historical data to identify patterns and distinguish genuine threats from false positives. An example is using AI algorithms for real-time updates integrating threat intelligence feeds, allowing a quick adjustment to evolving threats.
Another core aspect is automating security operation workflows, such as using AI tools to manage repetitive tasks like log analysis. For instance, this could involve deploying AI chatbots for real-time incident responses, significantly reducing response times. Additionally, the strategy emphasizes enhancing risk management through AI-driven risk assessments and real-time monitoring via visual dashboards, aiding organizations in maintaining a strong risk posture.
The strategies
⛳️ Strategy 1: Improve threat detection accuracy
- Implement machine learning models to analyse historical threat data and identify patterns
- Use AI algorithms to differentiate between genuine threats and false positives
- Integrate threat intelligence feeds to update detection models in real-time
- Continuously update AI models with recent data for increased accuracy
- Collaborate with threat analysts to refine model parameters and feedback loop
- Deploy anomaly detection systems to identify unusual patterns or activities
- Create a centralised dashboard to monitor detection accuracy metrics
- Conduct regular validation tests to ensure model performance
- Automate model training and deployment processes to maintain relevance
- Establish a feedback mechanism for analysts to report on model efficiency
⛳️ Strategy 2: Automate security operations workflows
- Map out existing security workflows and identify areas for automation
- Implement AI-based tools to automate repetitive security tasks such as log analysis
- Integrate automation scripts into Security Operations Centre (SOC) processes
- Develop playbooks for automated response actions to common security incidents
- Train security staff on using automation tools and incorporating them into workflows
- Employ AI chatbots for real-time incident response queries and recursive issues
- Utilise AI to prioritise incidents based on severity and potential impact
- Measure the reduction in time spent on manual security tasks
- Track incident response time and identify bottlenecks
- Review and optimise automated processes on a quarterly basis
⛳️ Strategy 3: Enhance risk management strategies
- Develop risk scoring models to evaluate potential threats and their impact
- Implement AI analytics to assess the vulnerabilities within the network infrastructure
- Integrate AI-driven risk assessments into the broader risk management framework
- Create visual dashboards for real-time risk monitoring and decision-making
- Regularly update AI models with emerging threat data to adjust risk assessments
- Involve cross-functional teams in risk management planning and response exercises
- Conduct periodic simulations of risk scenarios to assess the preparedness
- Benchmark risk posture relative to industry standards and competitors
- Identify and mitigate key dependencies like data availability and integrity
- Regularly update stakeholders on risk posture and necessary changes in strategy
Bringing accountability to your strategy
It's one thing to have a plan, it's another to stick to it. We hope that the examples above will help you get started with your own strategy, but we also know that it's easy to get lost in the day-to-day effort.
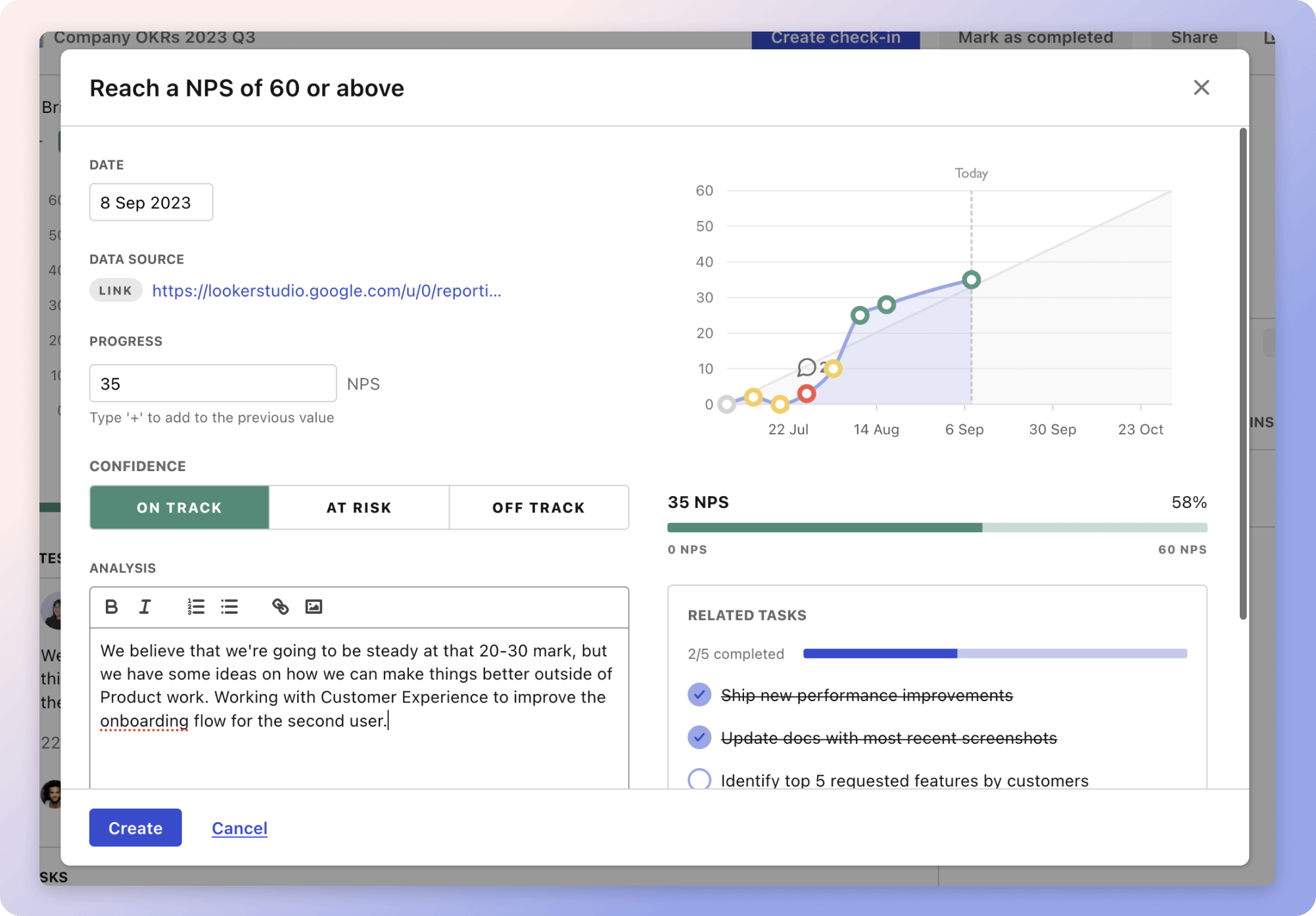
That's why we built Tability: to help you track your progress, keep your team aligned, and make sure you're always moving in the right direction.
Give it a try and see how it can help you bring accountability to your strategy.
